![On GPS spoofing of aerial platforms: a review of threats, challenges, methodologies, and future research directions [PeerJ] On GPS spoofing of aerial platforms: a review of threats, challenges, methodologies, and future research directions [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2021/cs-507/1/fig-4-full.png)
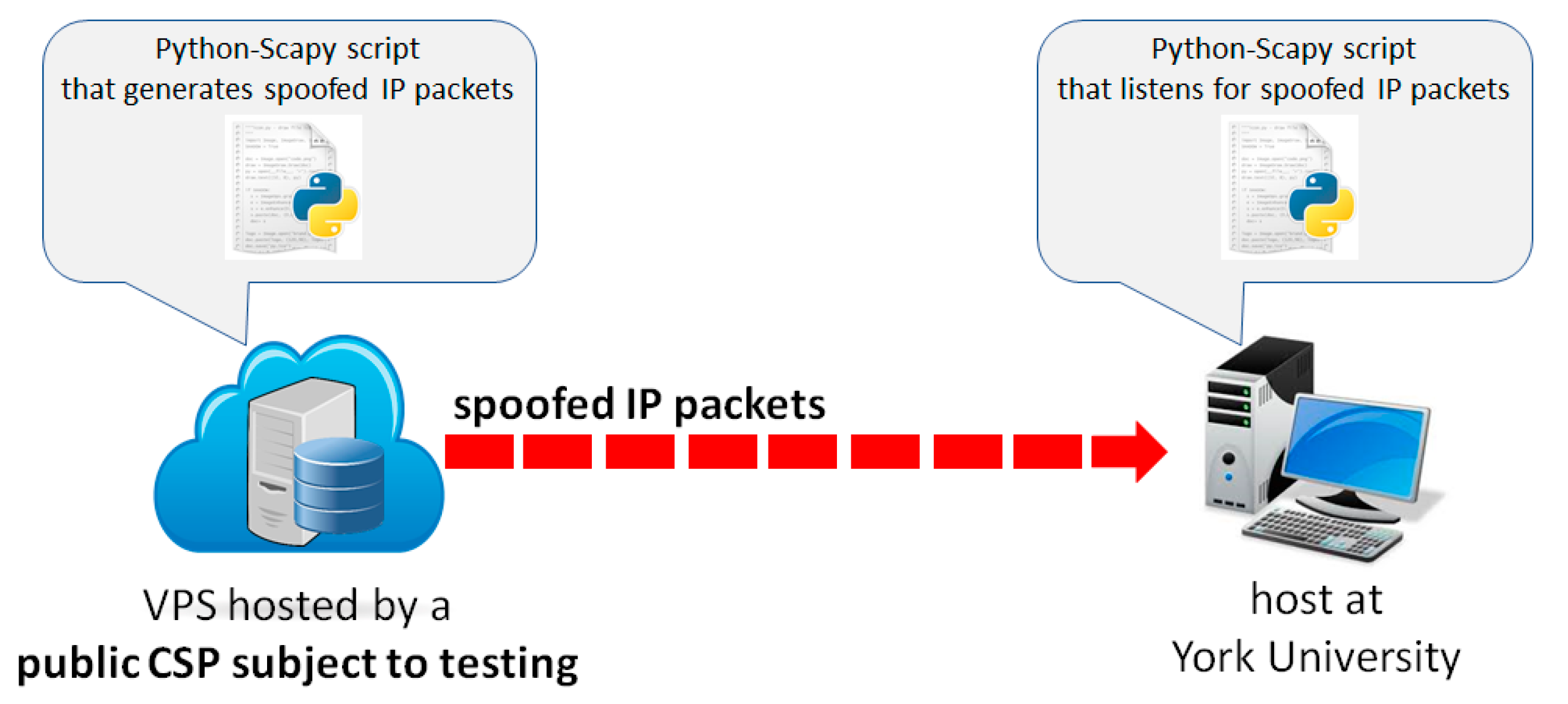
On GPS spoofing of aerial platforms: a review of threats, challenges, methodologies, and future research directions [PeerJ]

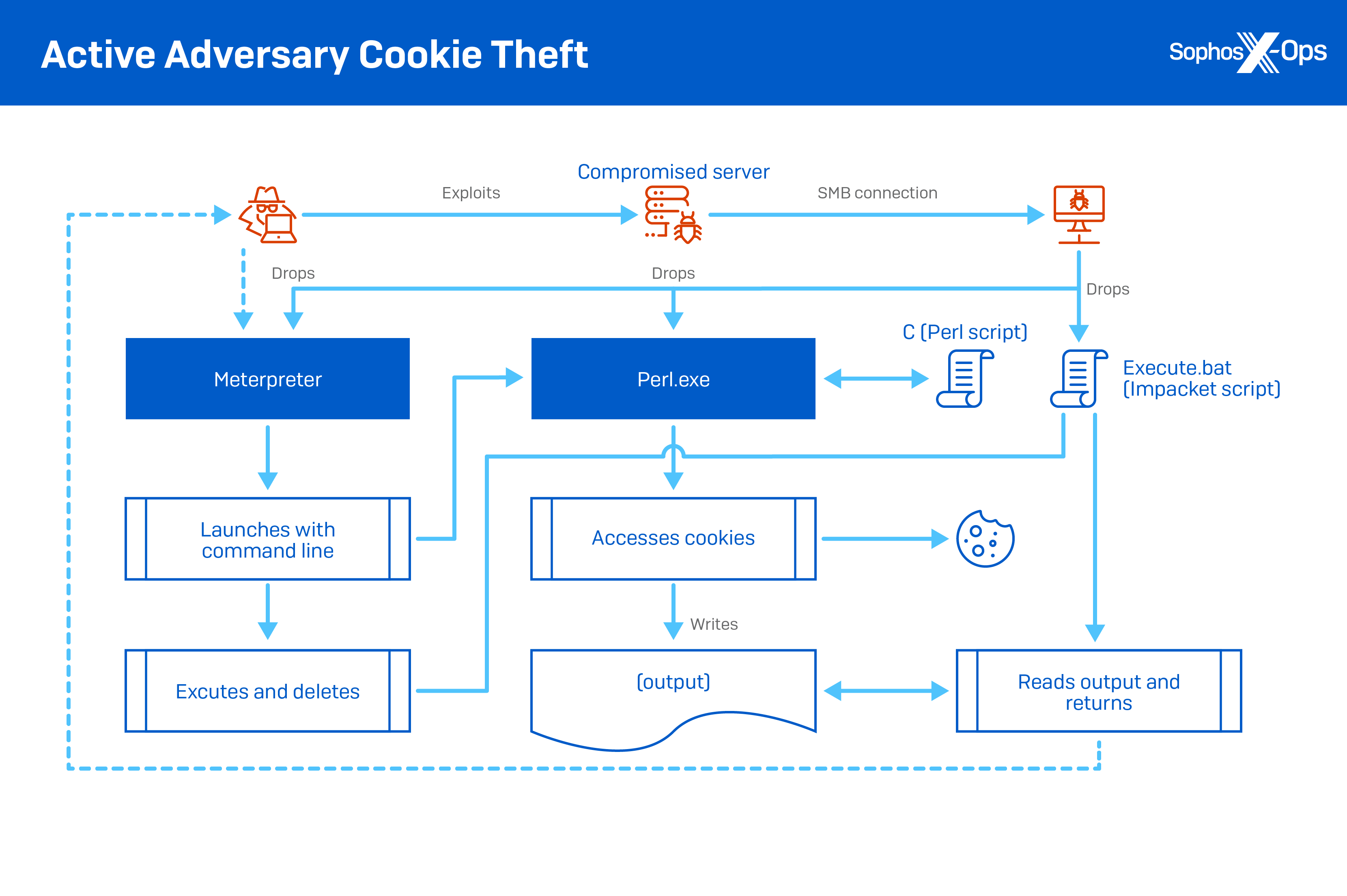
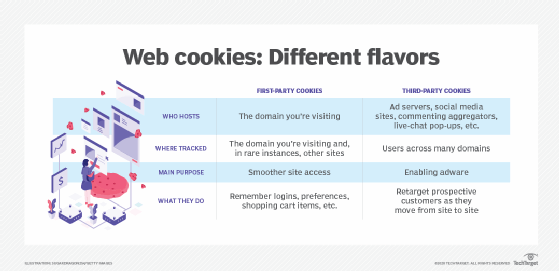
Cookies Resulting in Cross Border Transfers of Personal Data to the United States Draw Scrutiny from European Data Privacy Regulators | Health Law Advisor